Global Engineering
Education at your doorstep
Enrol in the 4-Year B.E. program at Chitkara University in India with an Academic Mentorship from Deakin University, Australia with an option to transfer in the third year of the coveted 4-Year Bachelor Engineering (Honours) Degree in Australia at Deakin University.
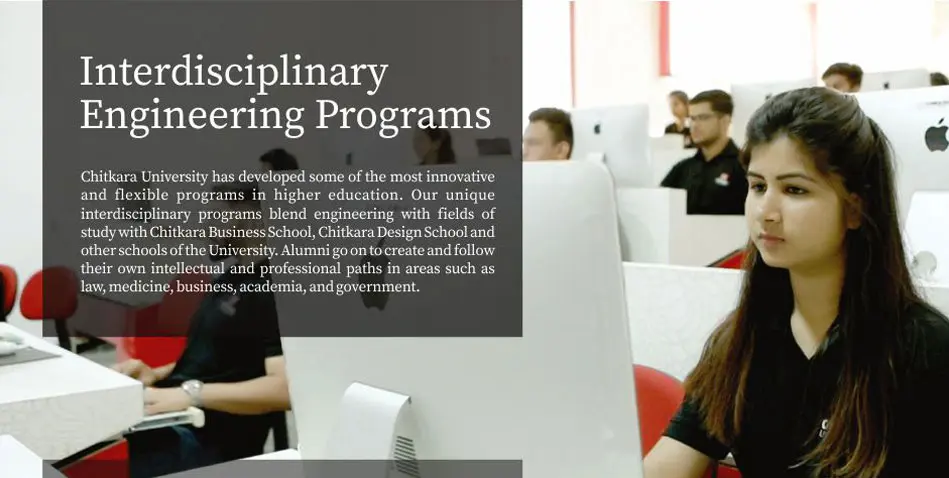
Software Engineering